How do hackers break into your technology environment? According to our penetration testing services team, it often comes down to one missing patch. How do you avoid this fate? Let’s step through a recent penetration test that illustrates the latest hacker techniques. We’ll share how the pentest team finds the security gaps and some critical steps that stop attackers in their tracks.
The target: a professional services firm. The IT team had recently updated their systems and said it was unlikely that the penetration testing services team would find anything, but they wanted to do their due diligence (turns out, that was a very wise move!)
The client provided a list of IP addresses which anyone on the Internet could scan—and nothing else. From there, it was game on.
The First Step: Reconnaissance
LMG’s penetration testing services team began by scanning the targeted computers to see which ones were actually responsive using the popular tool, nmap (which recently celebrated its 25th birthday). As professionals, LMG’s team always conducts multiple, comprehensive scans, beginning with the initial discovery sweep and continuing with an initial scan of top ports (to get quick results), a full TCP scan, UDP scans, and more. Next, we used our favorite vulnerability scanner, Nessus Professional, to scan the live systems for vulnerabilities.
Analyzing the attack surface, our ethical hackers quickly identified a computer that was missing a critical software patch—a VMWare Horizon View server. This popular software provides a virtual desktop infrastructure (VDI), enabling users to remotely log in to a hardened infrastructure. It is designed to support secure remote login. There were five VMWare Horizon View servers—but only four of them were fully patched.
One Critical Vulnerability
The last server was missing a critical software update that left it vulnerable to…. (drumroll)…. Log4Shell. For those of you that may have been hiding under a rock for the past year, Log4Shell exploits a vulnerability in the Apache Log4j library, which is widely used in software products around the world. Attackers can leverage this vulnerability to gain full remote access to the underlying systems. It has been dubbed “the worst computer vulnerability discovered in years.”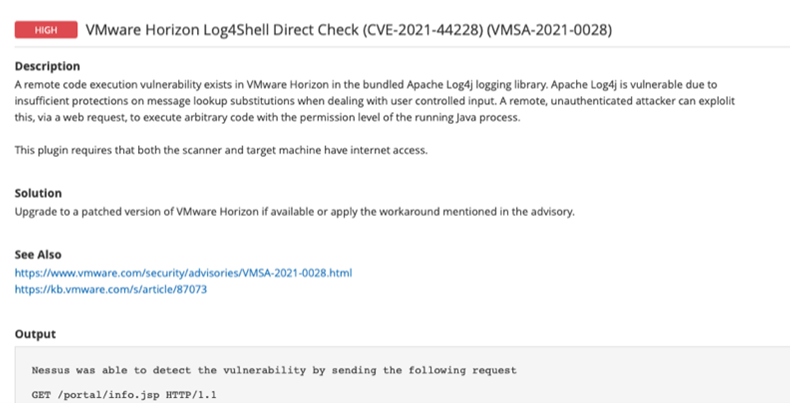
The IT team was sure they had patched their systems. The vulnerability, after all, had been patched for a year, and the staff made sure to apply it to all production systems. What they didn’t realize was that there was an old development server that was still on the network—unpatched. The IT team thought it had been decommissioned. No one knew it was even still connected to the Internet, and so no one had thought to check for patches.
This problem is all too common. For example, the major Equifax data breach, which leaked 145 million Social Security Numbers, was the result of a single server that was missing a patch for the well-known Apache Struts vulnerability.
The Penetration Testing Services Team Breaks In
LMG’s penetration testing services team exploited the vulnerable server using the open-source tool Log4jHorizon (read this blog for more on the Log4j vulnerability) From there, we had a command prompt with full administrative access to the server.
Attackers don’t stop at one server—they use their first point of access as a foothold to pivot further into your technology environment. “Once hackers have access to one system, it’s only a matter of time before they spread throughout your network,” said Tom Pohl, LMG Security’s Penetration Testing Team Manager.
Going After Credentials
Passwords and credentials are the keys to the kingdom. The ethical hackers’ next step was to steal any credentials from the hacked system, in order to use them to gain access to other servers and cloud accounts.
Today’s attackers often “live off the land,” leveraging common IT utilities rather than installing their own malware. This helps them evade detection while infiltrating your systems. LMG’s ethical hackers like to emulate real-world tactics. In this case, our penetration testing services team used a built-in Windows utility, reg.exe, to create a backup of three important registry hives—“SAM,” “SECURITY,” and “SYSTEM.”
After copying these registry hives to the hackers’ local computers, the ethical hackers used an open-source utility called “secretsdump.py” to get password hashes and other sensitive information. (A password “hash” is a cryptographically transformed version of your password, which is designed so it is very difficult for attackers to figure out your original password.)
Jackpot!
At this point, the penetration testing services team realized they had hit the jackpot. The booty included local administrative user hashes, domain computer account hashes, domain cached credentials, and more.
Using this highly sensitive stolen data, the ethical hackers could worm their way throughout the target’s internal network, and likely even login to cloud systems, using the following tactics:
- “Pass the hash” attacks, in which the hackers use the stolen NTLM hashes to log in to other servers and workstations throughout the internal network
- Cracking – the ethical hackers could feed the stolen hashes into superfast computers in order to recover the original passwords. LMG’s password cracking systems can guess billions of passwords per second, resulting in a high password recovery success rate. Once the original password was recovered, it could be used to directly log in to any internal systems or cloud accounts that use the same credentials. Today, many organizations use tools such as ADFS that join the internal domain to cloud services like Microsoft 365. This means that once a domain account is compromised, it can be used to break into both the local network and cloud systems.
The penetration testing services team quickly alerted the client to the critical issues and began working collaboratively to help strengthen the client’s systems.
4 Key Ways to Protect Your Systems
Missing patches are an all-too-common issue. As demonstrated, a single vulnerability can lead to a full takeover of your environment. Here are 4 key ways that you can protect your organization:
- Conduct continuous vulnerability scans – All organizations, from large to small, miss patches now and then. Sometimes patches don’t install properly, sometimes a computer is missed, and sometimes humans just misconfigure patching solutions. It’s important to monitor your attack surface by scanning your Internet-facing IP addresses routinely, and taking quick action to resolve any issues.
- Maintain an Accurate Inventory – In order to properly patch computers, you need to know that they exist. Ensure that your team maintains an accurate inventory of IT assets, including servers, workstations, network devices, and more. Routinely verify by scanning your IP address ranges to identify any unexpected systems.
- Validate your patches – Many organizations have automated patching systems that don’t always alert the right person when an error occurs. Make sure to verify that critical patches are installed correctly, either using patch management tools with built-in verification procedures, vulnerability scans, or (better yet!) both.
- Deploy EDR / XDR – Endpoint detection and response (EDR) systems, and their successors, extended detection and response (XDR) systems, typically include advanced AI and automation, which can alert when attackers are in your environment, even if they “live off the land,” and use common IT tools to spread.
The Takeaway
As you can see from the example in this blog, the security of your organization can come down to one missing patch. In addition to implementing the strategies above to reduce your risk, every organization should have a penetration test at least once a year. With the average worldwide total cost of a data breach reaching $4.35 million USD, with the average US cost of a breach reaching a staggering $9.4 million USD (the highest in the world), penetration testing is an inexpensive way to strengthen your security. The goal of a penetration test is to find ALL of your vulnerabilities. It simulates an attack and finds your security gaps before a criminal turns them into a data breach.
We hope you found this information helpful. Please contact the LMG Security team if you need a penetration test, help implementing these solutions, developing policies, testing your environment, or training your team. We’re ready to help.
Blog post courtesy of LMG Security.
